Higher Education & Research Universities
Research networks are open by design.
Visibility shouldn’t be optional.
University networks carry research traffic, student devices, clinical systems,
and cloud infrastructure — all on flat, open architectures
that can’t be locked down the way enterprise networks can.
NetFlow Optimizer gives IT and security teams full visibility
without restricting the open environment that research depends on.
2014
In production at universities
80–90%
SIEM ingest reduction
<1hr
Deploy time, no hardware
Trusted by



The Challenge
Three problems unique to university networks
Research universities face network challenges that don’t map to enterprise playbooks.
Open infrastructure, constrained budgets, and
decentralized governance create a distinct set of visibility problems.

Massive, Flat, Open Networks
Research universities run high-bandwidth, open networks by necessity — collaborative research, external partner access, and academic freedom mean you can’t segment and restrict traffic the way a corporate network can. That openness is the point. But it makes anomaly detection difficult without full flow visibility.

SIEM Cost on a Constrained Budget
Many universities run Splunk or Microsoft Sentinel — but on budgets that don’t scale with data growth the way enterprise budgets do. Raw NetFlow from a large university network generates massive ingest volumes that quickly become unaffordable, forcing teams to sample or exclude flow data entirely

Security Without Restriction
University security teams can’t apply the same controls as enterprise security. Blocking traffic, restricting ports, or requiring agents on every device conflicts with research and academic freedom. The answer is visibility — detecting anomalous behavior through flow analysis without interfering with legitimate activity.
HOW NFO HELPS
Full network telemetry — without touching the open architecture
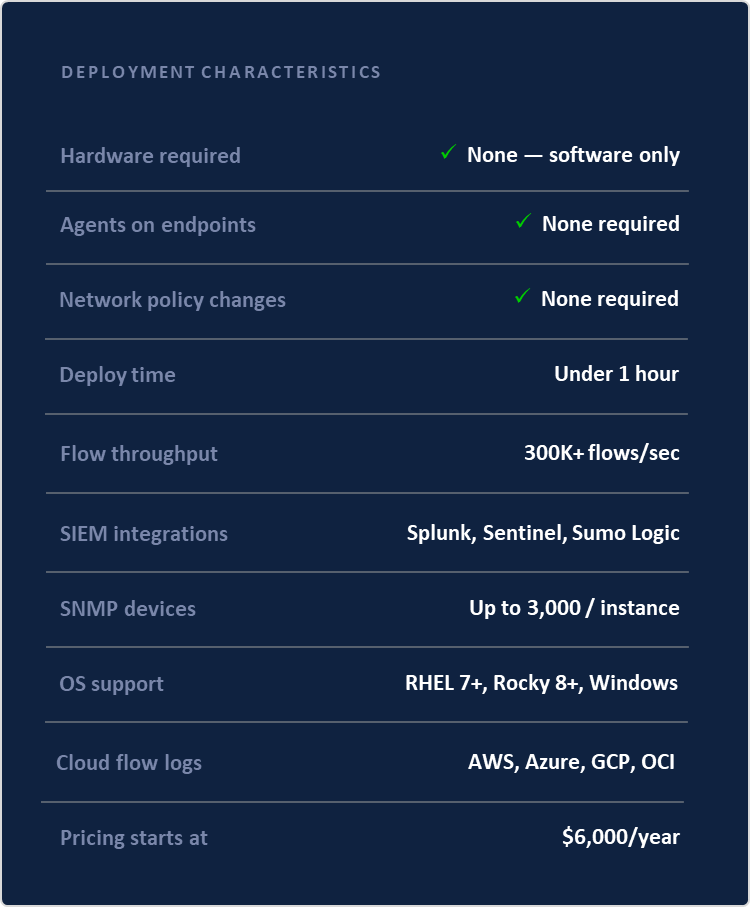
NFO is software-only and deploys in under an hour. It collects NetFlow from your existing routers and switches — no new hardware, no agents on endpoints, no changes to network policy.

Passive Flow Collection
NFO collects NetFlow, IPFIX, and sFlow from your existing network infrastructure. No agents, no taps, no configuration changes on research equipment. Visibility without touching the open architecture.

Anomaly Detection via SIEM
Enriched, normalized flow telemetry feeds directly into Splunk, Microsoft Sentinel, or Sumo Logic — enabling correlation rules and behavioral analytics that surface threats without blocking legitimate research traffic.

Identity-Enriched Flows
NFO resolves IP addresses to user identities via Active Directory — so security analysts investigate by person, department, or research group rather than raw IP addresses that change daily on a university network.

DDoS Detection
NFO’s built-in DDoS Detector uses proprietary ML to identify 31 attack types — volumetric floods, application-layer attacks, and low-and-slow resource exhaustion — without interfering with normal research traffic patterns.

Zero-Touch SNMP Device Monitoring
Automatically discovers and classifies every network device across your campus — switches, routers, wireless controllers, firewalls — and monitors device health without manual OID configuration or spreadsheet inventories.
Use Cases
How university IT and security teams use NFO
Security Operations
Threat detection without traffic restriction
Flow-based visibility surfaces malicious activity — data exfiltration, lateral movement, command-and-control traffic — without blocking or inspecting research data. Enriched records feed directly into SIEM correlation rules.
SIEM Cost Management
Full NetFlow coverage at an affordable ingest cost
NFO reduces Splunk or Sentinel ingest volume 80–90% before data reaches your workspace. Universities that couldn’t afford full NetFlow visibility can now ingest every conversation at a fraction of the raw cost
Network Operations
Visibility across the entire campus network
Real-time bandwidth analysis, top-talker identification, and application usage across your entire campus infrastructure — without sampling or blind spots. Capacity planning backed by actual traffic data.
Research Infrastructure
Monitor high-bandwidth research traffic non-intrusively
Research workloads generate traffic patterns unlike anything in enterprise environments — large data transfers, international collaborations, unconventional protocols. NFO monitors all of it passively without interfering.
Compliance & Audit
Network audit trail for compliance reporting
NFO’s NetFlow Recorder captures and stores flow data for forensic replay and compliance reporting. HIPAA for clinical research, FERPA for student data, and grant-specific data handling requirements are all supported.
Device Management
Automatic inventory of campus network devices
Zero-Touch SNMP Discovery automatically scans, classifies, and monitors every network device across your campus — including devices added by research groups without central IT involvement. Self-healing inventory, no spreadsheets.
Full network visibility for your campus.
Starting at $6,000/year.
Try NFO on your own network during the free trial period, or
talk to an engineer about your specific campus environment and flow volume.
