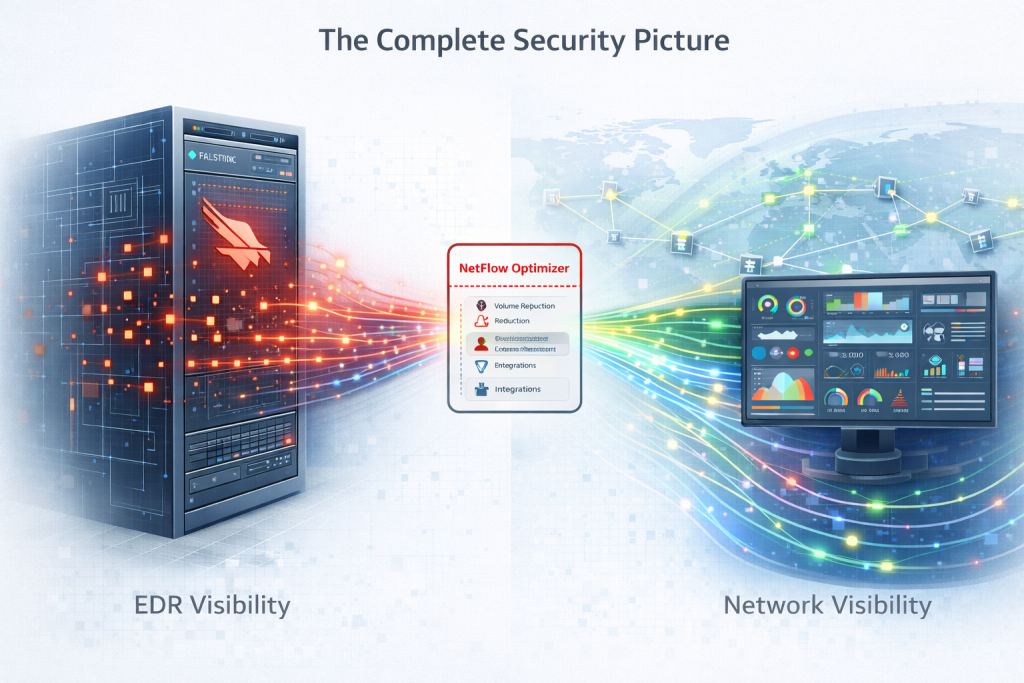
In the modern security stack, CrowdStrike Falcon has earned its reputation as a gold standard for Endpoint Detection and Response (EDR). It provides unparalleled visibility into process execution and local file activity. However, even the most powerful EDR platforms have an inherent limitation: the endpoint is not the network.
CrowdStrike excels at telling you what happened on the box, but gaining visibility into the “connective tissue” between those boxes remains a challenge. While CrowdStrike Falcon LogScale offers native ingest listeners for NetFlow/IPFIX, raw collection is often not enough for a proactive SOC. This is where the “Network Layer Blind Spot” hides — and where NetFlow Optimizer (NFO) turns raw logs into actionable intelligence.
Why Raw Collection Isn’t Enough
While CrowdStrike Falcon LogScale can ingest NetFlow records, raw ingestion presents significant hurdles for enterprise-scale security:
- The “Cloud Security” Hurdle: Native ingest listeners are primarily available for self-hosted environments. For organizations using Falcon LogScale (SaaS), sending raw, unencrypted UDP NetFlow over the public internet is a security risk. NFO acts as a secure, local gateway that aggregates and pushes enriched data via HTTPS.
- The Multi-Vendor Dialect Problem: Every hardware vendor implements NetFlow differently. If you have Cisco, Palo Alto, and AWS, raw collection forces your analysts to write complex, vendor-specific queries. NFO normalizes these formats into a single, standardized schema before they hit your dashboard — a process we detail in our Multi-Vendor Integrations Guide.
- The Context Gap: A raw flow log tells you 10.0.1.5 talked to 1.2.3.4. It doesn’t tell you who that user is. NFO enriches every record in real-time with Active Directory/Entra ID/Okta identities, turning a cryptic log into a clear narrative.
Filling the “East-West” Gap
When a threat actor gains a foothold on an endpoint, they move laterally. They want to move East-West across your data center to find high-value targets.
While CrowdStrike sees a suspicious process start, it may miss the network conversation if the target is an unmanaged device — like an IoT printer or industrial controller — that cannot host a Falcon agent. NFO provides visibility for the portions of your network that agents can’t touch, aligning with the Zero Trust Security Model.
NFO + CrowdStrike: A Unified Defense
For organizations running both Splunk and CrowdStrike, NFO is the missing piece. By delivering enriched, normalized network telemetry alongside Falcon’s endpoint data, you can:
- Validate EDR Alerts: Instantly see the network volume associated with a suspicious process.
- Trace Exfiltration: While EDR sees a file being read, NFO sees the 10GB of data actually moving laterally inside your network.
- Simplify Threat Hunting: Eliminate “query fatigue” by searching a single, standardized field (like src_ip or dest_port) across your entire hybrid environment, regardless of whether the data originated from a Cisco switch, a Palo Alto firewall, or an AWS VPC.
Achieve 360-Degree Visibility
The most effective security teams don’t choose between EDR and Network Visibility; they integrate them. By feeding NFO’s enriched network telemetry into your security platform, you provide the “Network Context” that endpoint agents cannot provide alone.
Don’t let your EDR blind spot become an attacker’s playground. High-fidelity network visibility is the missing link in your security stack. Enhance your CrowdStrike and Splunk investment today by eliminating lateral movement blind spots and streamlining your threat hunting.
Start Your Free Trialor Schedule a Personalized Demoto see how NFO delivers enriched network context directly into your SOC dashboard.
