Defeating the “Low and Slow”: Detecting Stealthy Data Exfiltration with Flow Analysis
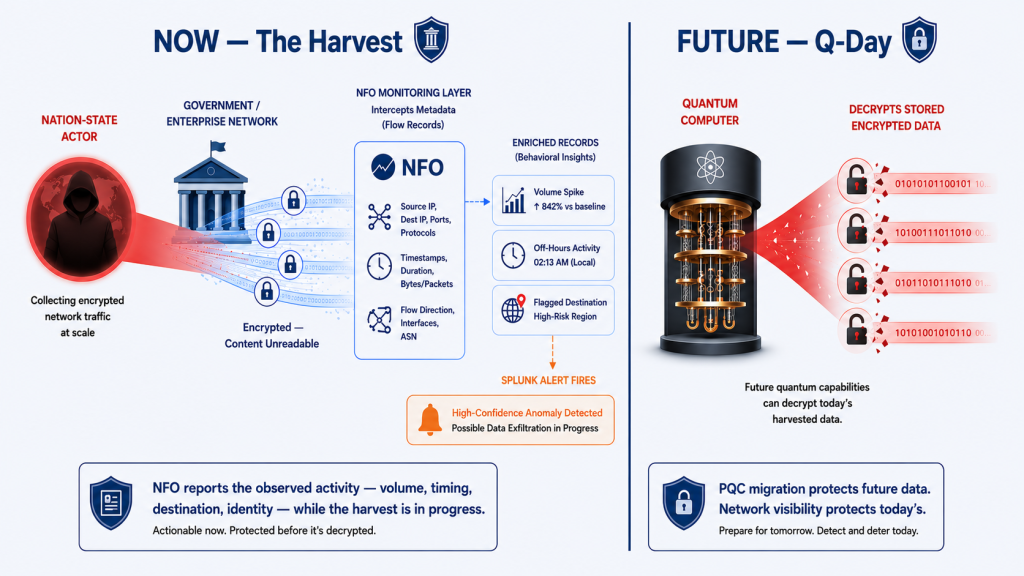
The security incidents that cause the most lasting damage are often the ones nobody notices […]
Defeating the “Low and Slow”: Detecting Stealthy Data Exfiltration with Flow Analysis Read more >>