Ask any CMMC Third-Party Assessment Organization (C3PAO) what they most commonly find missing in Level 2 assessments, and the answer is consistent: organizations know where their Controlled Unclassified Information (CUI) is stored. They do not know where it travels.
This distinction matters enormously. NIST SP 800-171 does not only require you to secure the systems that store CUI. It requires you to monitor, control, and audit the network communications that carry CUI between those systems — and to be able to prove, with evidence, that only authorized users and devices are part of those conversations.
Most organizations cannot produce that evidence on demand. They know their CUI file server exists and is hardened. They cannot show an assessor a user-attributed, time-stamped record of every network conversation that file server had last Tuesday.
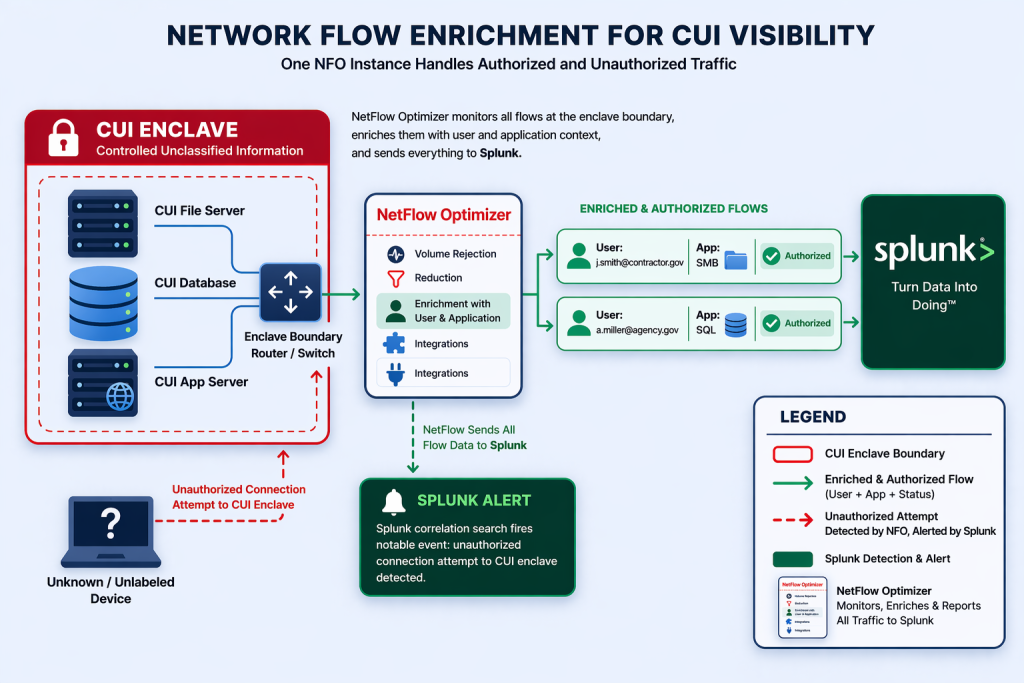
That is the gap NetFlow Optimizer (NFO) closes — not by replacing your data classification tools, DLP systems, or access controls, but by adding the continuous network-layer visibility that turns CUI protection from a policy into a provable, auditable practice.
What CMMC 2.0 Actually Requires for CUI Network Visibility
CMMC Level 2 maps directly to the 110 controls of NIST SP 800-171. Several of those controls specifically require organizations to monitor and audit the network communications involving CUI-handling systems — not just the systems themselves.
The controls assessors focus on most heavily in this area are:
| NIST Control | What It Requires — and Why Network Telemetry Is the Evidence |
| AU.L2-3.3.1 | Create and retain system audit logs to enable the monitoring, analysis, investigation, and reporting of unlawful or unauthorized system activity. Network flow records are among the primary evidence artifacts for this control — they are the continuous log of every communication a CUI-handling system initiates or receives. |
| AU.L2-3.3.2 | Ensure that the actions of individual users can be traced to those users so they can be held accountable. Raw NetFlow, IP addresses only, fails this control. Enriched NetFlow, with user identity resolved from Active Directory before it reaches your SIEM, satisfies it. |
| SC.L2-3.13.1 | Monitor, control, and protect communications at the external boundaries and key internal boundaries of organizational systems. Assessors will ask for evidence that boundary controls are active and effective — not just configured. Flow telemetry from CUI enclave boundaries is that evidence. |
| SC.L2-3.13.2 | Employ architectural designs, software development techniques, and systems engineering principles that promote effective information security. Flow telemetry validates that your network segmentation architecture is actually enforcing CUI enclave boundaries at runtime — not just on paper. |
| SI.L2-3.14.6 | Monitor organizational systems, including inbound and outbound communications traffic, to detect attacks and indicators of potential attacks. Continuous network flow monitoring of CUI-handling systems directly satisfies this control — and provides the detection record assessors require. |
The Problem with How Most Organizations Currently Handle This
The typical DIB contractor’s approach to CUI network visibility looks something like this: the CUI-handling systems are identified, placed in a dedicated VLAN or enclave, and protected by firewall rules. Access control lists define which users and systems are permitted. The SIEM receives Windows event logs from those systems.
This approach satisfies the access control configuration requirements. It does not satisfy the continuous monitoring and user-attributed audit trail requirements: because Windows event logs record local system activity, not network-layer communications. They tell you a user logged in. They do not tell you what network conversations that user’s session generated, where data moved, or whether a CUI-handling system communicated with an unauthorized destination.
When a C3PAO assessor asks: “Show me evidence that only authorized users and systems communicated with your CUI file server over the past 90 days” — a firewall ACL and a Windows event log cannot answer that question. A continuous, user-attributed, time-stamped network flow record can.
How NFO Creates a Continuous CUI Flow Map
NFO does not classify CUI. It does not replace your data loss prevention tools or your access control systems. What it does is provide continuous, enriched network telemetry from the infrastructure your CUI-handling systems already run on: the routers, switches, and firewalls whose flow data captures every network conversation those systems have. Read more about NFO’s government and public sector capabilities.
The result is an always-on, network-layer record of CUI system communications, enriched with the user and application context that NIST SP 800-171 requires for traceability.
1. Monitoring the CUI Enclave Boundary
Your CUI-handling systems live in a defined network segment: a VLAN, a subnet, or a dedicated enclave. The routers and switches at that boundary already generate NetFlow data for every packet that crosses it. NFO ingests that flow data and turns it into a continuous, searchable record of:
- Every system that communicated with a CUI-handling server
- Every external destination a CUI-handling system reached out to
- Every protocol and application used in those communications
- The volume and duration of each conversation
This is the boundary monitoring evidence SC.L2-3.13.1 requires. It is generated automatically, continuously, from infrastructure you already own.
2. Resolving User Identity Before the Data Reaches Your SIEM
The single most common failure point in CUI audit trail requirements is the lack of user attribution. An IP address communicating with a CUI server proves a connection occurred. It does not prove who made it.
NFO resolves this inside the pipeline, before data reaches Splunk or any other SIEM. Every flow record is correlated in real-time with Active Directory — mapping the source IP to the authenticated user account behind it. The enriched record that arrives in your SIEM reads:
“User: j.smith@contractor.gov • Source: 10.1.4.22 • Destination: CUI-FileServer-01 • Application: SMB • Duration: 4m 12s • Bytes Out: 247MB • 14:32 EST”
That single enriched record directly satisfies AU.L2-3.3.2 — the requirement that individual user actions be traceable to those users. It is the difference between a raw log and an audit artifact. For a deeper look at how identity enrichment transforms threat detection, see our post Beyond the IP: Why Identity-Enriched Threat Hunting is a Game Changer.
3. Detecting Unauthorized CUI Communications in Real Time
A continuous flow map of CUI enclave communications does more than satisfy audit requirements. It enables active detection of two categories of events that assessors specifically look for evidence of monitoring:
- Unauthorized internal access: A device or user account communicating with a CUI-handling system that is not on the approved access list. This appears in NFO’s enriched flow telemetry as an anomalous source communicating with a known CUI system IP. Security teams can build Splunk correlation searches against this data to surface these events as notable alerts.
- Unauthorized external communications: A CUI-handling system initiating a connection to an external destination: a cloud storage endpoint, a personal email service, or an IP flagged by threat intelligence. NFO’s GeoIP enrichment and threat intelligence scoring flag these in real time, before data has left the boundary.
Both categories directly satisfy SI.L2-3.14.6 — the requirement to monitor inbound and outbound communications for indicators of attack or policy violation.
4. Validating That Your Segmentation Actually Works
Network segmentation is a cornerstone of CUI protection. Most organizations have segmentation configured. Very few have continuous evidence that it is enforced at runtime.
NFO provides that evidence. Because it monitors the actual flow records crossing (or attempting to cross) your CUI enclave boundary, it generates a continuous, time-stamped record proving that your segmentation controls are blocking unauthorized traffic, not just that they are configured to do so. For organizations running formal Zero Trust micro-segmentation policies, see how NFO validates those policies in practice in our post Micro-Segmentation Validation: Using NFO to Prove Your Zero Trust Policy Works.
Making CUI Telemetry Actionable in Splunk
NetFlow Optimizer’s Splunk integration delivers enriched CUI enclave flow telemetry in CIM-compliant JSON format, indexed and immediately searchable. For CMMC-focused Splunk deployments, this enables three specific capabilities that directly accelerate audit preparation:
- Custom CUI traffic dashboards in Splunk: Real-time and historical views of all communications to and from CUI-handling systems can be built in Splunk using NFO’s enriched flow data, filterable by user, destination, protocol, and time window. Once configured, these dashboards give assessors a clear, on-demand view of CUI enclave traffic.
- Splunk-driven anomaly alerting: Splunk correlation searches written against NFO’s enriched flow stream can fire notable events when a CUI enclave IP communicates with an unauthorized source or destination. NFO provides the high-fidelity, user-attributed data that makes these searches accurate and low-noise — the alerting logic itself lives in Splunk, where your team defines and owns it.
- 90-day audit trail retrieval: Because NFO reduces raw flow volume by up to 80-90% before ingestion, long-term retention of CUI enclave flow records in Splunk is operationally and financially sustainable — without the storage costs that unoptimized NetFlow would generate.
For organizations running Splunk Enterprise Security inside a government environment or in Splunk Cloud’s FedRAMP-authorized environment, NFO’s on-premises pipeline ensures that enrichment happens inside your security boundary. The SIEM receives processed, attributed data — no raw CUI-adjacent telemetry ever leaves your environment.
What This Looks Like During an Actual Assessment
A C3PAO assessor conducting a CMMC Level 2 assessment of your network monitoring controls will typically ask for several specific evidence artifacts. Here is how the NFO + Splunk combination responds to each:
| Assessor Request | NFO + Splunk Response |
| Show me who accessed your CUI systems in the past 90 days. | Splunk dashboard filtered to CUI enclave IPs, showing user-attributed flow records with timestamps, application, and data volume for the full 90-day window. |
| Prove that your CUI enclave boundary controls are enforced, not just configured. | Continuous flow telemetry from the enclave boundary switches showing no unauthorized cross-enclave communications, with time-stamped records of blocked attempts where applicable. |
| Show me evidence that you actively monitor for unauthorized access to CUI systems. | Splunk correlation searches built on NFO’s enriched flow data, configured to alert when CUI enclave IPs are contacted by unauthorized sources. NFO supplies the continuous, attributed telemetry; Splunk executes the detection logic your team defines. |
| Did any CUI system communicate with an external destination outside your approved list? | GeoIP and threat-intelligence-enriched outbound flow records for all CUI enclave systems, filtered to external destinations, showing zero unapproved communications — or flagging any that occurred for immediate review. |
The Bottom Line: Compliance Requires Proof, Not Just Policy
Knowing where your CUI is stored is the starting point, not the finish line. CMMC Level 2 requires you to prove, continuously and with evidence, that your CUI-handling systems are communicating only with authorized users, applications, and destinations — and that you are actively monitoring for violations.
NetFlow Optimizer provides the network-layer visibility that makes that proof possible. By turning your existing network infrastructure into a continuous, user-attributed, boundary-monitoring sensor grid, and delivering that enriched telemetry into Splunk, NFO bridges the gap between a hardened CUI system and a defensible, audit-ready compliance posture. Learn more about our government and public sector solutions.
The assessor will ask what moved across your network, when, and who authorized it. NFO makes sure you can answer.
Ready to build an audit-ready CUI network monitoring posture? Contact us to speak with a NetFlow Logic engineer about your CMMC environment, or schedule a technical demo to see NFO and Splunk delivering CUI enclave telemetry in action.
Request a Quote | Schedule a Demo | Government Solutions | Start Free Trial
