When a security incident strikes – a breach, a data exfiltration, or a persistent malware infection – the clock starts ticking. Every second counts. In these high-stakes situations, security teams pivot from prevention to investigation, becoming digital detectives. Their most crucial tool? Reliable, detailed, and intelligible data. Without it, forensics becomes a frustrating guessing game, extending dwell times, increasing damage, and delaying recovery.

We’ve previously discussed how enriched and optimized NetFlow enhances network observability (Beyond Basic Monitoring: Why Enriched NetFlow is Your Key to True Network Observability) and even fuels AI-driven threat hunting (Automating Threat Hunting: How Optimized NetFlow Fuels AI-Driven Security Operations). Today, we shift our focus to the critical post-incident phase: how optimized NetFlow empowers high-fidelity network forensics and incident response.
The Nightmare of “Naked” NetFlow in Forensics
Imagine a crime scene. Now imagine that scene is chaotic, with crucial evidence scattered, obscured, or missing context. This is often the reality for security analysts relying on unoptimized, “naked” NetFlow data during an incident. While raw NetFlow provides fundamental information like source/destination IP addresses and ports, it often lacks the crucial context needed to build a clear narrative of what happened.
- Volume Overload: Terabytes of raw NetFlow data are overwhelming. Searching through this undifferentiated mass is like looking for a needle in a haystack, slowing down investigations significantly.
- Lack of Context: Without details like user identity, application names, or device types, an IP address remains just an IP address. Was that connection from a legitimate user’s laptop or a compromised server? Was it for a business application or a malicious service? Raw data offers no immediate answers, leading to more questions and dead ends.
- Fragmented Picture: Without a cohesive view, analysts piece together fragmented clues, making it difficult to understand the attack’s scope, lateral movement ([Internal Link to “Beyond the Firewall: How Enriched NetFlow Reveals Lateral Movement and Insider Threats”]), or the true root cause.
This results in slower root cause analysis, prolonged containment efforts, and an incomplete understanding of the attack chain, all of which contribute to higher incident costs and greater business disruption.

Optimized NetFlow: Your High-Fidelity Forensic Tool
Enter optimized NetFlow – a game-changer for incident response. By processing raw NetFlow data through solutions like our NetFlow Optimizer (NFO), it transforms from a burdensome data flood into a precise, high-fidelity forensic tool.
Here’s how enriched and optimized NetFlow provides the clear narrative you need:
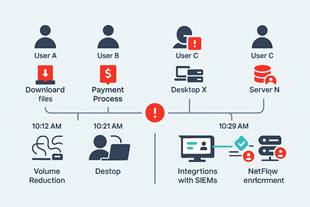
- Context is King: Our NetFlow Optimizer enriches raw flow data with crucial context. This means attaching user identities (who), application names (what), device details (from where), and even geographical information (where). When an incident occurs, you instantly know that “User Jane Doe’s laptop accessed a critical file server using an unusual communication channel,” instead of just “IP 192.168.1.10 connected to 10.0.0.5.” This immediate context drastically cuts down investigation time.
- Reduced Volume, Faster Searches: The NFO intelligently reduces the sheer volume of NetFlow data by aggregating redundant flows and removing meaningless data, like ephemeral client ports. This means your forensic tools and SIEMs have significantly less data to process, leading to lightning-fast queries and more efficient analysis. You’re searching a precise database, not an undifferentiated lake.
- Clear Narrative and Timeline: With enriched, reduced data, analysts can reconstruct the sequence of events with unparalleled clarity. You can easily trace lateral movement, identify initial compromise points, understand data exfiltration attempts, and pinpoint command-and-control communications. This clear narrative is vital for effective containment, eradication, and recovery.
- Integration Ready: Optimized NetFlow data is perfectly formatted for seamless integration with your existing security tools, including SIEMs, SOAR platforms, and threat intelligence feeds. This leverages your previous investments and creates a unified platform for incident investigation.
NetFlow Optimizer: Essential for Incident Preparedness
When an incident inevitably occurs, having the right data at your fingertips makes all the difference. Our NetFlow Optimizer is a critical component of any robust incident response plan. It ensures that when you’re faced with an attack, the data needed for a successful investigation is not only available but also intelligible, contextualized, and ready for immediate analysis.
Stop guessing in the aftermath of a breach. Start knowing precisely what happened, how it happened, and who was involved. Equip your incident response team with the high-fidelity NetFlow data they need to act decisively and restore security.
Contact us today to learn how NetFlow Optimizer can transform your incident response capabilities and request a personalized demo.
