
Your organization knows that a credential was used. What it often doesn’t know is what that credential did next.
Identity-based attacks are now the dominant initial access technique across enterprise and government environments. According to IBM X-Force, identity-based attacks account for 30% of all intrusions. Attackers don’t exploit vulnerabilities when phishing, credential stuffing, and MFA bypass give them legitimate-looking access. Once inside, they use those valid credentials to move laterally, escalate privileges, and stage exfiltration — all while appearing, to identity logs, as authorized users doing normal things.
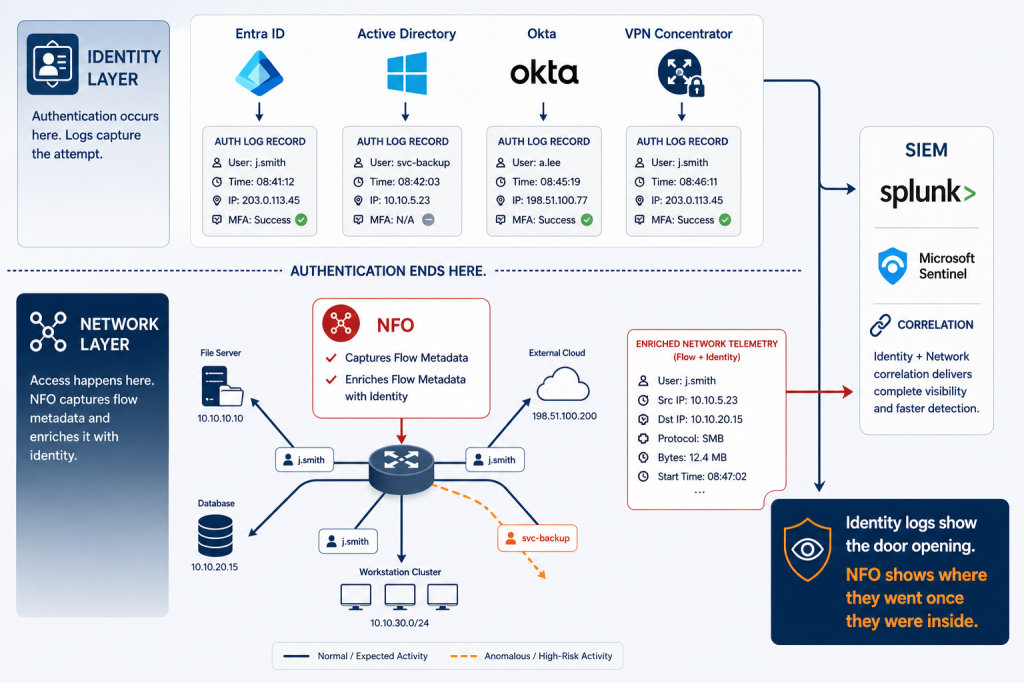
The security industry’s response has been Identity Threat Detection and Response (ITDR) — a category of tools that monitor identity providers like Microsoft Entra ID, Active Directory, and Okta for behavioral anomalies: impossible travel, privilege escalation, unusual authentication patterns. ITDR is a meaningful improvement over relying on IAM alone. But it has a structural blind spot that attackers exploit with increasing sophistication.
ITDR watches the door. It tells you who walked in, when, and from where. It does not follow them through the building.
What happens after authentication — which systems that credential accessed, what data it touched, where it sent traffic, what devices it communicated with — is a network-layer question. And most ITDR tools have no visibility into the network layer at all. That is the gap NetFlow Optimizer (NFO) closes.
What Identity Logs Tell You — and What They Don’t
Understanding the gap requires understanding what identity logs actually contain. When a user authenticates through Entra ID, Active Directory, or Okta, those systems generate a sign-in record that captures:
- Who authenticated (username, account)
- When they authenticated (timestamp)
- Where they authenticated from (IP address, device, geolocation)
- Whether MFA was satisfied
- Whether the authentication succeeded or failed
This is valuable data. It is also, critically, a record of the authentication event only. It does not capture what the authenticated session did on the network afterward. The moment credentials are validated and a session token is issued, the identity provider’s visibility effectively ends.
What the identity log cannot tell you:
- Which internal systems the authenticated user’s session connected to after login
- How much data was transferred, in which direction, and to which destinations
- Whether the session made lateral connections to other internal hosts
- Whether traffic was sent to external destinations inconsistent with the user’s role
- Whether the session behavior matched this user’s historical pattern
A compromised credential that authenticates normally and then moves laterally across twelve internal systems, accesses a file server, and stages 40GB of data for exfiltration will generate a clean authentication log in Entra ID. The identity log shows a successful sign-in. The network tells a completely different story.
The VPN Authentication Gap
There is a second, often overlooked identity visibility gap that is particularly relevant for hybrid and distributed environments: VPN authentication.
When a remote user authenticates through a VPN concentrator — whether using RADIUS, LDAP, or SAML — that authentication event is typically recorded in the VPN system’s own logs, and may or may not be correlated with Entra ID or AD sign-in events in your SIEM. More importantly, the VPN authentication record captures the same limited data as any other identity log: who connected, when, and from where.
What it does not capture is the network activity that followed the VPN connection. Once a user establishes a VPN tunnel, all subsequent traffic traverses your internal network and generates NetFlow records on your routers and switches. Those flow records are where lateral movement, anomalous internal access, and data staging are visible — but only if something is collecting and analyzing them.
NFO ingests flow data from the VPN concentrator’s network interfaces alongside flow data from internal switches and routers, enriching all of it with the same user identity correlation. The result: a unified, user-attributed view of post-authentication network behavior whether the session originated on-premises, over VPN, or from a cloud environment. For more on how NFO enriches flow data with identity context from AD, Entra ID, and Okta, see our data enrichment documentation.
How NFO Adds the Network Behavioral Layer
NFO enriches every network flow record with user identity in real time, before the data reaches your SIEM. It correlates source IP addresses with authenticated user accounts from Active Directory, Microsoft Entra ID, and Okta — mapping network behavior to named individuals continuously, without requiring manual lookups or post-hoc joins.
The result is a continuous, user-attributed record of network activity that answers the questions identity logs cannot:
| Identity Log Tells You | NFO + Identity Enrichment Adds |
| j.smith authenticated successfully at 09:14 from IP 10.1.4.22 | j.smith’s session made 23 connections to internal hosts in the 30 minutes following authentication, including 3 hosts outside her normal access pattern |
| VPN session established for contractor a.jones from external IP | a.jones’s VPN session transferred 8.4GB to an internal file server and initiated outbound connections to 2 new external destinations not seen in prior sessions |
| Service account svc-backup authenticated at 02:30 | svc-backup initiated connections to 14 hosts it has never previously communicated with, at 2x its normal data transfer volume |
| MFA bypass attempt detected for admin account | The admin account’s IP had already initiated internal port scans across 3 subnets in the 90 minutes before the MFA event |
Each row in this table represents a scenario where the identity log, in isolation, provides incomplete or misleading context. The network behavioral layer either confirms the threat, escalates its severity, or — in the last row — reveals that the attack was already underway before the identity alert fired.
Specific Detection Scenarios
Service Account Abuse
Service accounts are among the most frequently abused credentials in enterprise environments because they often have broad permissions, rarely trigger MFA challenges, and their authentication events blend into background noise. NFO’s identity enrichment maps service account activity to network flow records, making it possible to detect when a service account begins communicating with systems it has no business reason to access, at volumes inconsistent with its normal operational pattern.
Privileged Account Anomalies
When a privileged account — domain admin, security admin, cloud infrastructure admin — authenticates and then accesses systems or generates traffic inconsistent with the role’s operational profile, that deviation is visible in enriched flow data. NFO correlates the privileged account identity with flow records across the entire network, not just the endpoint where the account is logged in, providing a complete picture of what the privileged session actually did.
Data Staging Before Exfiltration
One of the most consistent precursors to data exfiltration is staging: large internal data transfers from a file server or database to a workstation or intermediate host before the data leaves the network. NFO’s identity-enriched flow data makes this visible as a named user transferring unusually large volumes from internal sources. Combined with the low-and-slow exfiltration detection techniques described in our post on data exfiltration, this provides a two-layer detection capability for the full exfiltration sequence.
NFO and ITDR: Complementary, Not Competing
NFO is not an ITDR tool and does not replace one. The distinction is important and worth being precise about:
| Layer | What It Covers | What It Misses |
| ITDR (Entra ID / AD / Okta monitoring) | Authentication events, sign-in anomalies, credential misuse patterns, MFA bypass, privilege escalation in the identity plane | Post-authentication network behavior — what the session did after the credential was validated |
| NFO identity-enriched flow telemetry | Post-authentication network behavior — connections made, data transferred, destinations reached, lateral movement — attributed to named users | Pre-authentication identity events — sign-in anomalies, MFA events, directory changes |
| ITDR + NFO in your SIEM | Complete identity threat picture: authentication anomalies correlated with post-authentication network behavior, attributed to named users, in a single SIEM environment | Nothing — this is the complete coverage model |
For organizations running Splunk Enterprise Security or Microsoft Sentinel, NFO’s identity-enriched flow stream is indexed alongside ITDR telemetry in the same environment. Correlation searches can join identity events with network behavior across the same user and time window — producing the kind of cross-layer detection that neither data source enables independently.
The Bottom Line: Identity Logs Tell You Who. Network Telemetry Tells You What They Did.
The identity is the new perimeter — but a perimeter is only as useful as the visibility you have inside it. Knowing that a credential was used, even knowing it was used anomalously, is not enough. The full picture of an identity-based attack requires understanding the network behavior that follows authentication: where the session went, what it accessed, what it transferred, and whether that pattern matches the user’s legitimate role.
NFO provides that picture by enriching every network flow record with real-time user identity from Active Directory, Microsoft Entra ID, Okta, and VPN authentication logs, and delivering a continuous, structured stream to your SIEM. Combined with your existing ITDR capability, it closes the gap between knowing a credential was used and knowing what damage was done — or is being done right now.
The identity log shows the door opening. NFO shows where they went once they were inside.
Want to see identity-enriched network flow telemetry in your SIEM? Start a free 60-day trial of NetFlow Optimizer or schedule a technical demo to see user-attributed flow data alongside your existing identity telemetry.
Start Free Trial | Schedule a Demo | Splunk Integration | Identity Enrichment Docs
