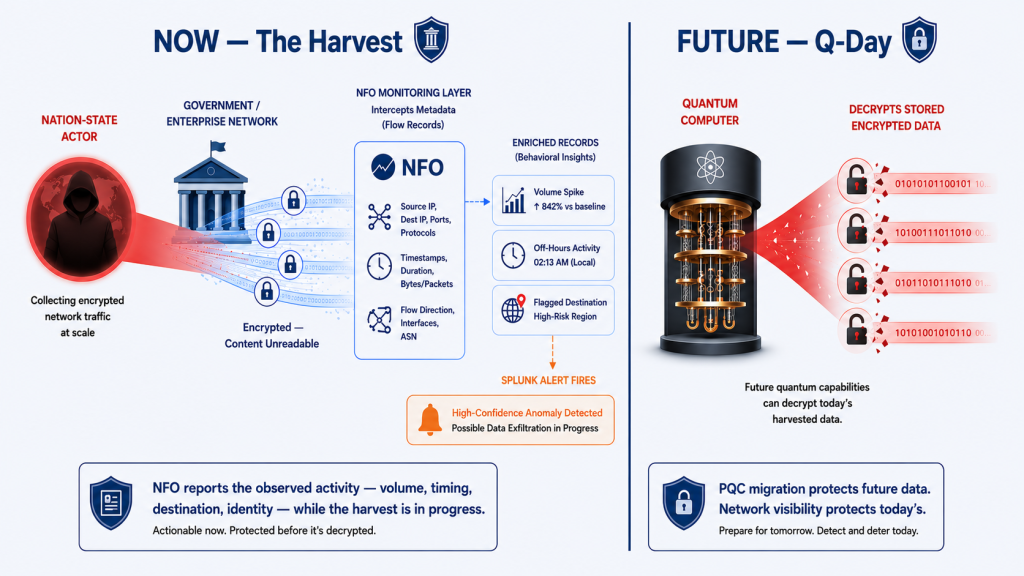
Your organization’s encrypted data is being stolen right now. Not because attackers have broken your encryption (they haven’t), but because they don’t need to. They are collecting it today and storing it until quantum computers make decryption possible. This strategy has a name: Harvest Now, Decrypt Later (HNDL). It is not a hypothetical future threat. It is an active, ongoing operation being conducted right now by nation-state actors with the resources, patience, and strategic intent to see it through.
The U.S. Department of Homeland Security, NSA, CISA, and NIST have all issued guidance explicitly premised on the assumption that adversaries are currently harvesting encrypted data with long-term strategic value. In January 2026, CISA issued new federal procurement guidance directing agencies to acquire only post-quantum cryptography-capable products in categories where they are widely available. In parallel, NIST’s post-quantum cryptography standards (FIPS 203, 204, and 205), finalized in August 2024, have become the de facto global gold standard for quantum-resistant encryption.
But here is the security gap that these standards do not address: migrating to post-quantum cryptography protects data you encrypt from today forward. It does nothing to protect data that has already been harvested. The breach is already in motion. The question is whether you can detect it.
The vulnerability does not occur on Q-Day, the future date when quantum computers can break encryption. It occurs today, at the moment your data is exfiltrated. Network visibility is the only layer that can catch HNDL-style operations while they are happening.
Understanding the HNDL Threat Model
HNDL attacks are patient, methodical, and deliberately designed to avoid detection. Understanding how they operate is essential to understanding what network telemetry can and cannot detect.
Who Is Doing This
Nation-state actors with advanced signals intelligence capabilities represent the primary threat. China’s quantum research investment is documented and substantial; the National Endowment for Democracy has specifically identified China’s HNDL strategy as a major concern. Russia’s intelligence services have similar collection capabilities. Both have the infrastructure to intercept traffic at scale, the storage capacity to archive it indefinitely, and the institutional patience to wait years or decades for quantum decryption to mature.
The targets are organizations whose data has a long confidentiality lifespan: government agencies managing classified communications and national security data, defense contractors handling CUI and program information, financial institutions with transaction histories and trading strategies, and healthcare organizations with genomic and patient data. For these organizations, data intercepted today may remain strategically valuable a decade from now.
What the Attack Looks Like at the Network Layer
This is where HNDL becomes a network security problem rather than purely a cryptographic one. The harvesting phase (the active collection of encrypted data) generates network activity that is detectable by network flow telemetry, even though the content of the encrypted traffic is not readable.
HNDL harvesting operations typically manifest as one or more of the following network-layer patterns:
- Sustained bulk outbound transfers: Large volumes of encrypted data moving from internal systems to external destinations over extended periods. The payload is encrypted and unreadable, but the flow metadata (volume, duration, destination, frequency) is visible in NetFlow records.
- Off-hours exfiltration patterns: Transfers timed to avoid peak operational hours, when anomalous traffic is less likely to be noticed by NOC staff. Flow data captures timestamps and duration, making temporal anomalies detectable.
- New or anomalous egress destinations: Traffic to cloud storage endpoints, unusual geographies, or IP ranges not previously seen in the organization’s baseline. GeoIP-enriched flow records surface these immediately.
- Encrypted tunnels to unexpected endpoints: VPN or TLS connections to destinations outside the organization’s approved external communication inventory. Even when the tunnel content is encrypted, the flow record shows source, destination, protocol, and volume.
- Low-and-slow incremental collection: Sophisticated HNDL operations deliberately spread transfers across weeks or months to stay below volumetric detection thresholds. Flow duration and frequency analysis over long observation windows is the primary technique for detecting these campaigns.
The critical insight: post-quantum cryptography addresses the ‘decrypt later’ half of the threat. Network flow visibility addresses the ‘harvest now’ half, the phase that is already happening and the only phase where defenders can intervene.
Why Encryption Makes the Network Layer More Important, Not Less
A common misconception is that encrypted traffic is invisible to network monitoring. This is true at the content layer, but it is fundamentally false at the network behavioral layer.
Network flow telemetry captures the metadata of every communication — source, destination, protocol, port, byte count, packet count, and duration — regardless of whether the payload is encrypted. This metadata is the behavioral fingerprint of an HNDL-style operation. Attackers cannot hide it without eliminating the exfiltration itself.
Consider what a flow record reveals about an encrypted transfer that a content-inspection tool cannot see:
| What Is Encrypted | What Flow Metadata Shows | What NFO Adds |
| The content of the data being transferred | Volume transferred, duration, frequency of transfer | NFO delivers volume, duration, and frequency fields to Splunk. Splunk detects anomalies against the established baseline for this host. |
| The identity of the user initiating the transfer | Source IP address | NFO resolves user identity from Active Directory: j.doe@big-bank.com |
| The nature of the destination | Destination IP address | GeoIP, ASN, and threat intelligence scores added to every external destination IP, even when exfiltration routes through legitimate cloud infrastructure. |
| The timing pattern of the operation | Flow timestamps across days and weeks | Continuously time-stamped flow records enable detection of recurring transfer patterns to the same destination across extended observation windows. |
Each of these data points is available in NFO-enriched network telemetry delivered to Splunk. None of them requires decryption. Together, they constitute the behavioral signature of an HNDL-style operation, visible and detectable while the harvest is still in progress.
How NFO Supports Detection of HNDL-Style Exfiltration Activity
NFO ingests raw NetFlow and IPFIX data from your existing routers, switches, and firewalls, enriches every flow record with user identity, application context, threat intelligence, and GeoIP data, and delivers a continuous, structured stream to your SIEM. Against HNDL-style exfiltration activity, this pipeline provides four visibility capabilities, in roughly descending order of applicability:
1. Temporal Pattern Analysis: Detecting Low-and-Slow Campaigns
The most distinctive characteristic of nation-state HNDL operations is patience. Data is collected slowly, over weeks or months, specifically to stay below volumetric thresholds. NFO delivers continuously time-stamped, user-attributed flow records that enable detection of recurring transfers to the same destination across extended observation windows, even when each individual event appears unremarkable. This is the technique most directly suited to the HNDL adversary model.
2. Volumetric Anomaly Detection
Bulk data exfiltration requires moving large volumes of data. NFO enriches every flow record with byte counts, duration, and user identity, providing the data foundation that upstream analytics tools need to detect when a host or user account is transferring significantly more than their established baseline, particularly to external destinations.
3. New Destination Discovery
HNDL operations require establishing a collection endpoint. The first time a sensitive system communicates with a previously unseen external destination, that event is visible in NFO’s flow telemetry. When combined with high volume or off-hours timing, first-contact events to new external IPs are a useful early-warning indicator of staging activity.
4. Threat Intelligence and Destination Context
NFO scores every external destination IP against threat intelligence feeds and adds GeoIP and ASN context before the record reaches your SIEM. This provides useful signal for less sophisticated operations. It is worth noting that advanced nation-state actors deliberately route through legitimate cloud infrastructure to avoid reputation-based detection, so this layer is most effective as one input among several rather than a primary detection method.
The Federal Compliance Dimension
For federal agencies and DIB contractors, the HNDL threat intersects directly with active compliance obligations, not future requirements. The federal PQC transition is already underway:
- NIST FIPS 203, 204, and 205, finalized August 13, 2024, establish the post-quantum cryptography standards that federal agencies and their contractors are expected to adopt. These standards address the “decrypt later” phase.
- CISA January 2026 procurement guidance directs federal agencies to acquire only PQC-capable products in categories where they are available. This is the supply chain pressure point that reaches DIB contractors.
- NSA CNSA 2.0 mandates that all new National Security Systems acquisitions be CNSA 2.0 compliant by January 1, 2027. Existing NSS equipment must phase out non-compliant algorithms by 2030, with full CNSA 2.0 compliance across NSS required by 2031.
- CMMC 2.0 AU and SC control families require continuous monitoring of network communications and retention of audit logs that support investigation of unauthorized activity — obligations that apply regardless of whether that traffic is encrypted.
The gap these mandates leave unaddressed is the “harvest now” phase that is already in progress. PQC migration makes future encrypted data quantum-resistant. It does not detect or stop the active collection of today’s encrypted traffic. Network flow monitoring is the complementary layer that addresses the phase of the attack that is happening right now.
For organizations building their CMMC assessment evidence package, enriched NetFlow telemetry — user-attributed, threat-intelligence-scored, and continuous — supports evidence collection for the AU.L2-3.3.1 and SC.L2-3.13.1 controls that assessors examine for network monitoring capability. For a detailed breakdown, see CUI on the Wire: How NetFlow Telemetry Maps and Monitors CUI Flows.
The Bottom Line: Post-Quantum Migration Is Necessary But Not Sufficient
Every federal agency and DIB contractor with a PQC migration roadmap is doing the right thing. Transitioning to quantum-resistant encryption is essential and urgent. But the migration timeline extends to 2033 for most systems, and the harvesting is happening now.
The data being exfiltrated today over encrypted connections will still be encrypted when Q-Day arrives. PQC migration protects what you encrypt after deployment. It cannot protect what has already been taken.
The only defense against the harvest phase is detecting it while it is in progress, and that requires network-layer behavioral visibility that sees what encrypted content cannot hide: the volume, timing, destination, and identity patterns that distinguish a nation-state HNDL-style operation from normal encrypted business traffic.
For government and DIB organizations building that visibility, NFO provides the enriched network flow telemetry, delivered on-premises inside your security boundary with zero data egress, that makes HNDL behavioral detection possible in Splunk. Learn more about our government and public sector capabilities.
Ready to add network behavioral visibility to your post-quantum defense posture? Schedule a technical demo with a NetFlow Logic engineer, or download our Government Solution Brief to see how NFO supports federal and DIB security requirements.
Schedule a Demo | Government Solution Brief | Start Free Trial | CUI on the Wire Blog
