And What Actually Fixes It
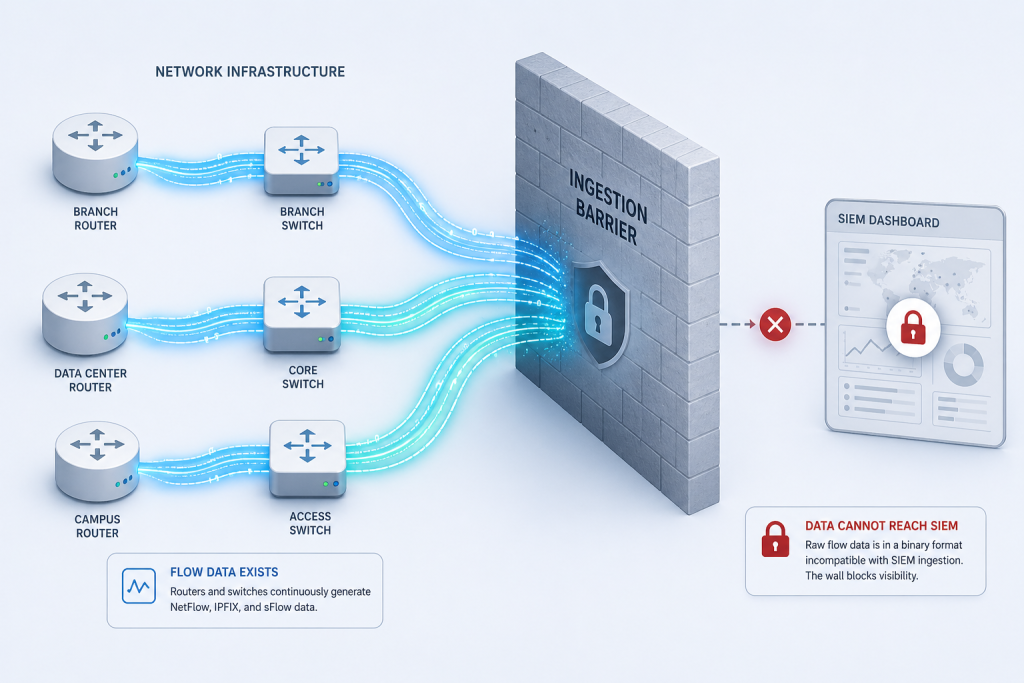
Network flow data (NetFlow, IPFIX, sFlow) is among the most valuable telemetry available to security and network operations teams. It is also, in its raw form, almost impossible to operationalize in a SIEM.
The reason is not a SIEM limitation. It is a data reality: raw NetFlow is binary, extremely high-volume, and completely un-enriched. Every router, switch, and firewall on your network generates it continuously, with every conversation summarized as a flow record: source IP, destination IP, port, protocol, byte count, duration. At enterprise scale, that means hundreds of thousands of flow records per second. Those records contain no usernames, no application names, no threat context: only IP addresses, bytes/packets count, and port numbers.
This is why the vast majority of organizations running Splunk, Microsoft Sentinel, or any major SIEM today have made a simple, pragmatic decision: they do not ingest NetFlow into their SIEM at all. Not because they don’t recognize its value, but because the raw format makes it unworkable.
This post explains exactly why NetFlow fails in every SIEM, what a complete solution actually requires, and what becomes possible when the problem is solved correctly.
The Real Choice: Properly Processed NetFlow, or No NetFlow at All
It is tempting to frame network flow data as a cost problem: too much volume, too expensive to ingest. But for most SIEM environments, the actual situation is more fundamental. The question is not how to reduce NetFlow volume in a SIEM. The question is how to get any NetFlow into a SIEM in a usable form.
Raw NetFlow presents three characteristics that make it impractical to ingest directly.
1. It Is Binary
NetFlow records are exported from routers and switches in a compact binary format, designed for efficient network transmission, not for human-readable analysis. Most SIEMs cannot ingest raw binary data. Without an external processing layer to decode and convert them first, NetFlow simply never enters the index at all.
Even when a NetFlow collector decodes the binary format, what arrives is still just IP addresses and port numbers. “10.4.2.17 talked to 185.220.101.45 on port 443 for 4.2 seconds” tells a security analyst almost nothing without context. Decoded is not the same as usable.
2. It Is Extremely High-Volume
A single enterprise-grade router can generate tens of thousands of flow records per second. Across a distributed network with dozens of routers, switches, and firewalls (each reporting NetFlow for every conversation they handle), the aggregate daily volume runs into hundreds of gigabytes for a mid-sized enterprise and terabytes for large government or enterprise environments.
Critically, much of this volume is redundant by design. When a single packet crosses three switches on its way to its destination, all three switches generate a NetFlow record for the same conversation. Multi-hop duplication, combined with the ingress/egress double-reporting common in many router configurations, means raw NetFlow volume often overstates the actual number of unique network conversations by a factor of three to five. Ingesting it raw means either a massive licensing cost increase or aggressive sampling that destroys forensic value. Neither is acceptable.
3. It Is Un-Enriched
A raw NetFlow record identifies endpoints by IP address. It does not tell you who was using that IP address, what application generated the traffic, whether the destination is known to be malicious, or what country the external connection reached.
In a SIEM environment built for security detection and investigation, a data source that delivers only IP addresses and byte counts requires significant additional processing (lookup tables, joins, enrichment pipelines) before it produces anything an analyst can act on. For most organizations, that processing overhead is the final barrier that makes raw NetFlow impractical.
The practical outcome of these three characteristics is consistent: security teams recognize the value of flow data, evaluate ingesting it into their SIEM, conclude that the raw format is unworkable, and abandon the effort. The network visibility layer that the SIEM could provide goes unrealized.
What a Complete Solution Actually Requires
The solution is not a better SIEM connector or a cheaper ingest tier. It is transforming the data before it enters the SIEM, at the point where transformation is possible without destroying fidelity. Specifically, that means four things happening in sequence before a flow record reaches your SIEM.
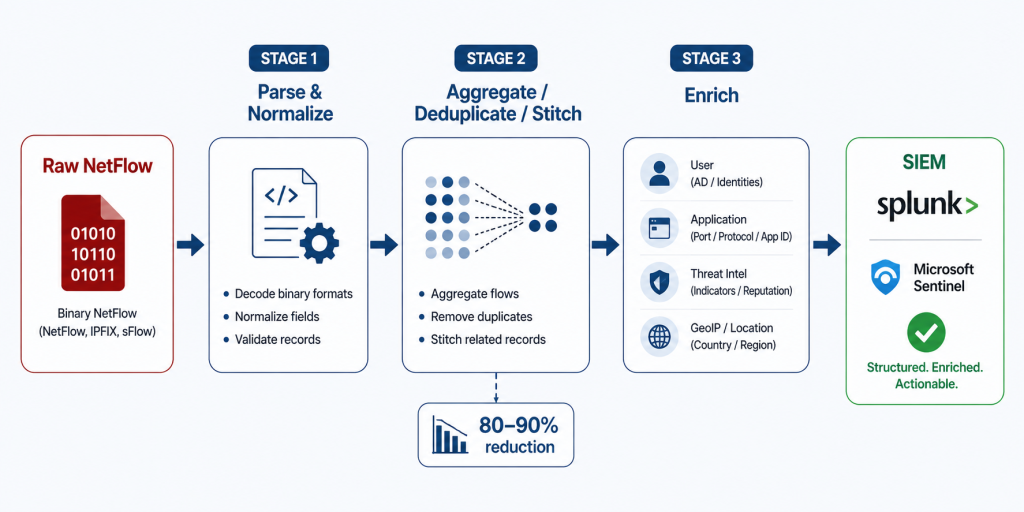
1. Parse and Normalize: From Binary to Structured, SIEM-Ready Output
Raw binary NetFlow records (across all major formats including NetFlow v5, v9, IPFIX, sFlow, and J-Flow) must be decoded and normalized into structured output delivered to the SIEM as JSON or syslog key=value pairs. This single step transforms an incompatible binary stream into indexed, searchable data. Every field (source IP, destination IP, protocol, port, byte count, duration) becomes a discrete, queryable field the moment it lands in the index.
For Splunk environments specifically, this means CIM-compliant output that works with existing correlation searches, dashboards, and Splunk Enterprise Security out of the box: no custom sourcetypes, no schema mapping.
2. Aggregate, Deduplicate, and Stitch: Eliminate Redundancy, Preserve Fidelity
Three complementary techniques reduce the volume of flow data delivered to the SIEM, without discarding analytically valuable information.
Aggregation combines flows that share the same key attributes (source, destination, protocol, and port) into a single summarized record, dramatically reducing record count while preserving the full picture of network activity.
Deduplication eliminates the multi-hop redundancy inherent in enterprise networks. When the same conversation is reported independently by multiple devices (an access switch, a distribution switch, and a core router), deduplication identifies these as perspectives on the same flow and consolidates them into one authoritative record.
Flow stitching reconstructs bidirectional conversations from separate ingress and egress records, replacing two half-records with a single complete entry that includes full byte counts, duration, and directional context.
The combined effect of these three techniques is what makes full-fidelity NetFlow in a SIEM sustainable, not by discarding data, but by eliminating the structural redundancy that inflates raw volume without adding analytical value. Done correctly, this reduces total ingest volume 80–90% while retaining every security-relevant flow.
3. Enrich: Add the Context That Makes NetFlow Actionable
This is the step that transforms NetFlow from a network metric into a security intelligence source. Before each flow record reaches the SIEM, enrichment appends the contextual metadata that makes it immediately usable by analysts and detection rules alike.
A properly enriched flow record arriving in a SIEM includes:
- User Identity: Real-time correlation with Active Directory, Okta, or Microsoft Entra ID maps every source IP to the authenticated user account behind it. The SIEM receives a named user (not an IP address), eliminating identity lookups at query time.
- Application Name: Layer-7 application context derived from the DPI and classification engines built into your existing network devices (Cisco NBAR2, Palo Alto App-ID, Fortinet FortiOS). Analysts work with “Salesforce,” “Office 365,” or “BitTorrent” rather than anonymous port/protocol pairs, including for encrypted traffic where port-based resolution fails entirely.
- Cyber Threat Intelligence: Every flow cross-referenced in real time against curated reputation feeds to detect communication with botnets, malware distributors, and TOR exit nodes.
- GeoIP and ASN: Country, city, and Autonomous System Number data for every destination, enabling geographic filtering, alerting on traffic to sanctioned regions, and compliance reporting without additional lookup tables.
- Reverse DNS (FQDN): IP addresses resolved to hostnames using existing DNS infrastructure, replacing abstract addresses with recognizable internal names (e.g., hr-portal-prod.local).
The enriched record that arrives in the SIEM is categorically more useful than the raw record. It is immediately searchable by user, application, destination country, threat score, and hostname. Correlation searches run against it without additional joins. Dashboards render with named users and applications rather than IP addresses.
4. Deliver in the SIEM’s Native Data Model
Output must be formatted to match the SIEM’s data model natively (Splunk CIM, Microsoft Sentinel ASIM), so existing detection rules, dashboards, and correlation searches work against network data without retooling. The integration point is a single data feed in a format the SIEM already understands.
When all four steps happen upstream of ingest, the SIEM finally receives something it can use: a manageable volume of structured, enriched, identity-mapped network telemetry. That is not NetFlow optimization. That is NetFlow enablement. For most organizations, it is the first time network behavior data has ever been actionable inside their security stack.
What This Unlocks: Detection Capabilities That Didn’t Exist Before
With properly processed NetFlow indexed in a SIEM, a set of detection and investigation capabilities become available that are simply unavailable without network flow telemetry, regardless of how many other data sources are already indexed.
| Capability | Without NetFlow in SIEM | With NFO-Enriched NetFlow |
| Lateral movement detection | Not possible: no east-west network visibility | Full east-west traffic, correlated with user identity and time |
| Exfiltration detection | Blind to network-layer data transfers | Large/sustained outbound transfers visible by user, destination, volume |
| C2 beaconing | Encrypted traffic invisible | Beaconing pattern detection even through encrypted flows |
| Forensic reconstruction | Gaps wherever no endpoint log exists | Complete network conversation history for every device |
| Compliance evidence (CMMC, NIST, FISMA) | No network communication audit trail | User-attributed network records ready for assessors |
None of this requires new SIEM infrastructure. It requires NetFlow data that the SIEM can actually consume.
For more on specific detection use cases, see The Network Layer CrowdStrike Can’t See, The Ransomware “Pre-Flight” Check, and CUI on the Wire.
Deployment: What It Actually Takes
The common assumption is that adding a new data source at enterprise scale is a months-long project. For raw NetFlow, that assumption is correct: the integration, normalization, and enrichment work is significant. For pre-processed, enriched NetFlow delivered in SIEM-native format, it is not.
For organizations with existing NetFlow infrastructure (a NetFlow collector already receiving flows from network devices), first data in Splunk or Sentinel typically arrives in under an hour. No new parsing. No schema mapping. The integration point is a single data feed in a format the SIEM already understands.
For organizations without existing NetFlow collection, add the time to configure flow export on network devices, typically a half-day for a network engineer familiar with the environment.
The Real Reason Most Teams Haven’t Done This Yet
It is not skepticism about the value of network telemetry. Every security architect knows network data matters. Nation-state actors who bypass endpoint detection still generate network flows.
The reason is that every prior attempt to get NetFlow into a SIEM ran into the three walls described above (binary format, volume, and no enrichment) and the cost and complexity to solve all three simultaneously, in-house, was not justified given everything else on the roadmap.
That calculation changes when all three problems are solved upstream, before the data reaches the SIEM, at a volume and cost that does not require a new ingest budget line.
If your organization has NetFlow being generated by network infrastructure (and virtually every enterprise network does) that data is currently your most valuable untapped security telemetry source. The network layer is generating a continuous record of every connection in your environment. It is just not reaching your SIEM.
It is time to use it.
Ready to add network telemetry to your SIEM?
Schedule a technical demo with a NetFlow Logic engineer to see enriched NetFlow visibility in action, or start a free 60-day trial and index your first enriched NetFlow data in under an hour.
Start Free Trial | Schedule a Demo | Splunk Integration Details | NFO Documentation
